Protecting Your Android-Based Smartphone Form Wireless Threats

Modern mobile phone users are shifting to smartphones and that fact puts a really high priority to the security of those mobile devices. It is widely known that smartphones are often used in various business affairs and that's why they sometimes contain some sensitive information. Those gadgets also gather your personal information and they can probably share it with evildoers. That's probably the main reason why mobile operational system's security has faced new, pretty high demands.
It may sound wild, but Android mobile operational system was cosidered to be the most safe and secure operational system. But with the development of the OS itself and its massive spreading the quantity of viruses and other malicious applications has rosed significantly. That's why today we will try to tell you how to make sure that the information that is stored at your Android smartphone is 100% safe.
Wireless networks
The first thing you can do here is to pay attention to wireless networks, regardless what are you trying to connect, the connection itself may be really dangerous. You should know that Wi-Fi networks are dangerous by their nature, they may be really vulnerable to various hacks and exploits. There are even mobile apps, designed for hacking wireless connections, so evildoer will need just a tablet or even a simple smartphone to be able to hack your mobile phone using Wi-Fi. It is also vital to check your smartphone's settings, because lots of them try to connect any network they can reach by default. It will be really helpful if you will turn Wi-Fi module of every time you don't need it. Or simply use a portable Wi-Fi jammer to block all wireless connections in the area.

Blusnarfing
Also such an obsolete technique as Blusnarfing is worth mentioning. The term itself means hacking various mobile devices using Bluetooth. Previously it was rarely used due to its inconvenience: hacker had to stay within 10 meters (30 feet) radius from the target, because it was the range of Bluetooth reception. But now it gains its popularity, because the working range of Bluetooth has been enlarged. Sometimes hackers may even use highly sensitive unidirectional antennas to accomplish those hacks remotely. But it is really simple to protect yourself form that. Not many people are using those connections in their daily life, so it will be better to turn it of. But if you need it sometimes – simply set it to “non-discoverable” mode by default. Also, we should mention that pickpockets use Bluetooth to look for expensive mobile devices at public places.
Malicious applications
And now we came to the main security issue of all Android-based gadgets – malicious applications. Most of those viruses are rather primitive and their main goal to send messages to short phone numbers or assign you to services that cost you additional money. Their advanced versions may send their copies to your contact list. Such often pretend to be popular apps like Skype or Angry Birds and attract users with adds-free or other features. We should mention that all of those malicious apps for Android will request permissions for sending messages and dialing phone numbers.
But sometimes there are really dangerous mobile apps that are able no only to steal your money, but gather you personal information as well. Usually those applications request permissions to access your browsing history, contact list and the physical memory of the device. Also it will try to get the permission for unlimited Internet access. If you see that an applications that has nothing to do with Internet services asks for unlimited Internet access – try to avoid it.
Also mobile apps that can dial phone numbers can possibly turn your mobile phone into an eavesdropping bug, that's the main reason why many offices or business centers have GSM jamming devices in their conference halls to ensure the safety of corporate information.
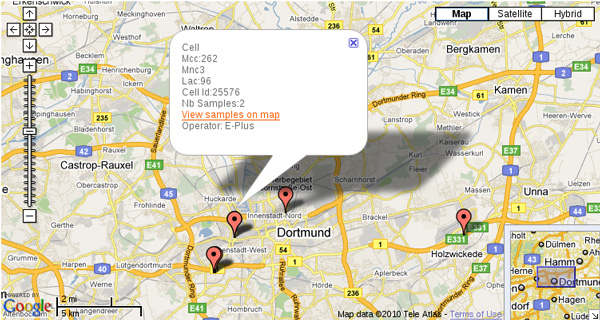
Also there is a separate family of malicious mobile applications that are able to track the locations and movement of your mobile device, using GPS as well as cell tower triangulation. Those mobile applications will ask permissions for accurate GPS coordinates access and coarse location, based on a cell network data. Also tracking apps will require an unlimited internet access.
How to avoid installing dangerous apps?
We at jammer-store.com can assure you that it is quite easy to protect your mobile device from the mobile threats we have described above. Try to avoid installing applications from untrusted sources, also you should remember that any mobile application will require your direct permission for all of its activity and by analyzing them you will be able to detect and avoid the most dangerous ones.
We hope that this short note will help you to protect your Android smartphone from the most widely spread mobile threats. Try to protect your personal information, because nowadays its has a really high price.






