May I Have That Approval, Or How Malware Uses Permissions On Android

Many are concerned about the protection of modern smartphones, so this topic deserves special attention. Now the FBK office has published a report on crimes connected to smartphones. It is now comprehended that the Android functioning technique is associated with many vulnerabilities. That is why you should use modern antivirus software for protection.
We have prepared the most insecure licenses your gadget uses. You should read the list carefully. Don't allow programs to access features they don't need. You should take care of your safety as much as possible.
Dialing phone numbers and sending messages
This allows you to use dialer and message apps. Many dangerous programs use such data to extort money from other people. If the program does not need a phone or messages, do not give such access.
Memory access
As a result, the program can use all the data on your machine. It can easily read and write all data. Many programs use these consents, but you should carefully monitor them to limit them if necessary.
Access to search history
Some programs request access to the search history and browser. If a questionable app asks for such access, you should deny it.
Access to the magazine
This license permits you to view technique descriptions. It contains various confidential information. There are no access exceptions.
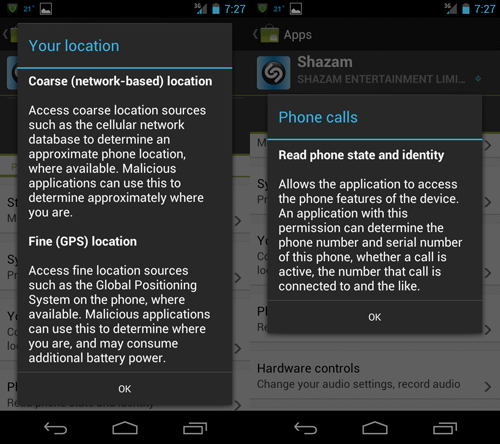
Phone status scan
This is necessary so that applications can go offline. This can create issues with saving your place and tracking data.
Determination of the exact location
This necessary permission allows apps to use information from maps or other apps. Some use the data to track you.

Location search
Some programs also use mobile phone triangulation to determine location.
Internet access
It affects the internet usage of the app. This is necessary for many problems, but not all, so you must watch for possible viruses.
Installing programs
This permission allows you to install programs. In this case, a virus is possible that will damage all files.
Jammer Store specialists offer the opportunity to get acquainted with modern jammers to secure your data. Take advantage of available opportunities on time. A universal jammer 2G, 3G, and 4G, which is highly effective for protection, will also be helpful.






